

|
Tools for Online Privacy |
|
 Having recently read and reviewed Edward Snowden's
Permanent Record,
here I'm going to survey some of the tools individuals can use to
attempt to reclaim a bit of their privacy in the face of ubiquitous
mass surveillance by governments and technology companies. This is not
intended to be an encyclopedic survey of the field, which is vast,
complicated, and constantly changing. Instead, this is an introduction
intended to point readers toward tools and approaches, many of which I
have used myself, discuss trade-offs between security and convenience,
and provide links for further research. The various topics are largely
independent of one another, and are discussed in no particular
order.
Having recently read and reviewed Edward Snowden's
Permanent Record,
here I'm going to survey some of the tools individuals can use to
attempt to reclaim a bit of their privacy in the face of ubiquitous
mass surveillance by governments and technology companies. This is not
intended to be an encyclopedic survey of the field, which is vast,
complicated, and constantly changing. Instead, this is an introduction
intended to point readers toward tools and approaches, many of which I
have used myself, discuss trade-offs between security and convenience,
and provide links for further research. The various topics are largely
independent of one another, and are discussed in no particular
order.
At this writing, the most widely used Web browser is Google's Chrome, with a market share around 65% which is expected to grow to more than 70% by the end of 2019. Chrome is famous for “phoning home”: every site you visit, link you follow, search you perform, and choice you make from the suggestions it so helpfully provides you is potentially reported back to Google headquarters. This is stored in a dossier maintained about you, especially if you have, as you're encouraged to, signed the browser in to your Google Account. That's how they manage to show you advertisements so exquisitely (or sometimes humorously) targeted based upon your online activity. But you don't have to be paranoid to worry about the consequences of, dare I say, such a permanent record being used against you should you come to the attention of the enforcers of good-think who abound in Silicon Valley.
 Fortunately, there are alternatives.
The Brave browser,
developed by Brendan Eich, himself a victim of Silicon Valley
oppression, uses the same Chromium engine as Google Chrome, but puts
security as a high priority. It does not track you, does not phone
home, automatically elides intrusive advertisements and trackers
embedded in Web pages you view, and often, by eliminating the clutter,
loads pages substantially faster than Chrome and Apple's Safari,
reducing mobile data charges. For even greater privacy, you can
open browsing tabs which route your queries through the Tor network
(which will be described in greater detail below), which hides your
identity and location from sites you visit and encrypts all
intermediate traffic to thwart snoopers and sniffers. Brave runs on
Linux, Windows, macOS, Android, and iOS (Tor browsing is presently
available only on Brave desktop platforms).
Fortunately, there are alternatives.
The Brave browser,
developed by Brendan Eich, himself a victim of Silicon Valley
oppression, uses the same Chromium engine as Google Chrome, but puts
security as a high priority. It does not track you, does not phone
home, automatically elides intrusive advertisements and trackers
embedded in Web pages you view, and often, by eliminating the clutter,
loads pages substantially faster than Chrome and Apple's Safari,
reducing mobile data charges. For even greater privacy, you can
open browsing tabs which route your queries through the Tor network
(which will be described in greater detail below), which hides your
identity and location from sites you visit and encrypts all
intermediate traffic to thwart snoopers and sniffers. Brave runs on
Linux, Windows, macOS, Android, and iOS (Tor browsing is presently
available only on Brave desktop platforms).
 The
Tor browser was developed by the Tor
project and is a Web browser which always goes through the Tor network
(like a Tor tab in Brave). It is available for Linux, Windows, macOS,
and Android (using the Tor network, which, at this writing, is not
available in the Android version of Brave), and does not require you
to install Tor on your computer. One annoyance in using Tor all the
time is that you never know from which exit node your request will
reach a Web site, and when communicating with sites which “geolocate”
based upon the IP address from which a request originated, you may
find yourself confronted with a page in Japanese or Korean if your
exit node happens to be in those countries.
The
Tor browser was developed by the Tor
project and is a Web browser which always goes through the Tor network
(like a Tor tab in Brave). It is available for Linux, Windows, macOS,
and Android (using the Tor network, which, at this writing, is not
available in the Android version of Brave), and does not require you
to install Tor on your computer. One annoyance in using Tor all the
time is that you never know from which exit node your request will
reach a Web site, and when communicating with sites which “geolocate”
based upon the IP address from which a request originated, you may
find yourself confronted with a page in Japanese or Korean if your
exit node happens to be in those countries.
 The
Chromium
browser is the open-source foundation of Google Chrome, and
consists of just the browser without all Google's tracking. Many
widely-used Linux distributions provide packages which allow it to be
installed and automatically updated. But note that it will invite you
to sign into a Google account: if you do so, you are compromising
your privacy.
The
Chromium
browser is the open-source foundation of Google Chrome, and
consists of just the browser without all Google's tracking. Many
widely-used Linux distributions provide packages which allow it to be
installed and automatically updated. But note that it will invite you
to sign into a Google account: if you do so, you are compromising
your privacy.
![]() In
the early days of the Web, data were sent “in the clear” where anybody
could snoop. Today, sites increasingly use the secure
HTTPS
protocol, which encrypts data sent to and from Web sites with the
Transport Level Security (TLS)
(formerly Secure Sockets Layer, or SSL) protocol. When connected to
a site using HTTPS, your browser's address bar will usually show
“https:” in the URL and/or a lock icon to indicate a secure connection.
Many sites, including Fourmilab, automatically promote all
connections from users with browsers that support it (which are
the overwhelming majority of those used today) to this secure protocol.
But some sites don't do this, and while they allow secure connections,
if you arrive there via a link which doesn't specify “https:” use
insecure communications for your session.
In
the early days of the Web, data were sent “in the clear” where anybody
could snoop. Today, sites increasingly use the secure
HTTPS
protocol, which encrypts data sent to and from Web sites with the
Transport Level Security (TLS)
(formerly Secure Sockets Layer, or SSL) protocol. When connected to
a site using HTTPS, your browser's address bar will usually show
“https:” in the URL and/or a lock icon to indicate a secure connection.
Many sites, including Fourmilab, automatically promote all
connections from users with browsers that support it (which are
the overwhelming majority of those used today) to this secure protocol.
But some sites don't do this, and while they allow secure connections,
if you arrive there via a link which doesn't specify “https:” use
insecure communications for your session.
HTTPS Everywhere is a browser extension, developed by the Electronic Frontier Foundation and Tor Project, which automatically forces connections to sites to which you connect that support the HTTPS protocol to secure mode. HTTPS Everywhere is available for the Chrome/Chromium, Firefox, Opera, and Brave desktop browsers and Firefox for Android, and can be installed from the browser's Extension, or Add-ons, or whatever they call downloadable features, menu. In Brave, HTTPS Everywhere is built in and enabled by default.
 Regardless of which Web browser you
use, if you're using Google for searches, you're creating a record of
queries which may be used against you. Say goodbye to Google and switch to
DuckDuckGo,
a free search engine which does not store your personal information,
search history, or what links you clicked in search results. You can
use DuckDuckGo directly from its search page, linked above, or
configure many (but not all) browsers (including Brave and Chromium)
to send queries you type in the address bar there instead of to Google.
I find that DuckDuckGo provides very high quality search results—it
isn't entirely up to the level of Google, but that's because Google is
tailoring results for you based upon its snooping on your online
activity and they aren't doing that. I'm more than willing to
read a little further down in the search results to know my every
search isn't being archived.
Regardless of which Web browser you
use, if you're using Google for searches, you're creating a record of
queries which may be used against you. Say goodbye to Google and switch to
DuckDuckGo,
a free search engine which does not store your personal information,
search history, or what links you clicked in search results. You can
use DuckDuckGo directly from its search page, linked above, or
configure many (but not all) browsers (including Brave and Chromium)
to send queries you type in the address bar there instead of to Google.
I find that DuckDuckGo provides very high quality search results—it
isn't entirely up to the level of Google, but that's because Google is
tailoring results for you based upon its snooping on your online
activity and they aren't doing that. I'm more than willing to
read a little further down in the search results to know my every
search isn't being archived.
![]() Google mail (Gmail) is free, fast,
and convenient, but they're reading all your mail and storing it
forever—think about that and its possible consequences.
ProtonMail,
based in Switzerland, provides end-to-end encryption when communicating
with other users of the system, and a less convenient means for
encrypted communications with users of other mail hosts. End-to-end
encryption means that ProtonMail never sees the messages that pass
through it in the clear, and does not have the keys to decrypt them.
The service keeps no IP logs which might be used for traffic analysis.
Free accounts with 500 Mb storage and up to 150 messages per day are
available. For €4/month, you get 5 Gb of storage, 1000 messages a
day, 5 E-mail aliases, encryption to external addresses, and the
ability to use your own E-mail address and domain name.
Google mail (Gmail) is free, fast,
and convenient, but they're reading all your mail and storing it
forever—think about that and its possible consequences.
ProtonMail,
based in Switzerland, provides end-to-end encryption when communicating
with other users of the system, and a less convenient means for
encrypted communications with users of other mail hosts. End-to-end
encryption means that ProtonMail never sees the messages that pass
through it in the clear, and does not have the keys to decrypt them.
The service keeps no IP logs which might be used for traffic analysis.
Free accounts with 500 Mb storage and up to 150 messages per day are
available. For €4/month, you get 5 Gb of storage, 1000 messages a
day, 5 E-mail aliases, encryption to external addresses, and the
ability to use your own E-mail address and domain name.
Frequently, you're required to supply an E-mail address to complete “registration” on a Web site which you may need to access just once to get something for which you're looking. If you use your main E-mail address, you may be inadvertently signing up for endless spam from the site which you can't turn off. A Disposable (or Temporary, or “Burner”) E-mail address is created on the fly by any one of a number of services, many of which are free, which you can use to register on the site, receive its registration confirmation, and reply, but which will go away after a specified time interval (anywhere from minutes to months, depending on the service). Once the address is deleted, any spam sent there will disappear into the bit bucket. You shouldn't use burner addresses for sites from which you may have to recover your password in the future, as the address to which the recovery would be sent will no longer exist, but for those snooper sites that just want to harvest E-mail addresses, they are an excellent way to protect your main mailbox.
 Signal is a free and open
source private messaging system which provides SMS-style text chat,
group conversations, transmission of images, video, and computer
files with end-to-end encryption (data appear in the clear only on
the devices of the sender and recipient, and are not stored). Voice
and video calls may be made using the same encryption, with no long
distance fees. There are no advertisements or tracking in the
software. Signal is available for Android, iOS, Debian-based Linux,
macOS, and Windows, and may be built from source code for other Linux
and Unix-like platforms. In order to activate Signal, you must have
a public telephone number upon which you can receive an activation
code. This need not be the mobile number of the device on which you
run Signal, and may be a land line. Once you have activated Signal on
a mobile device, you can then pair your desktop to it. Signal has
been endorsed by Edward Snowden (who is a regular user of it) and by
security guru Bruce Schneier.
Signal is a free and open
source private messaging system which provides SMS-style text chat,
group conversations, transmission of images, video, and computer
files with end-to-end encryption (data appear in the clear only on
the devices of the sender and recipient, and are not stored). Voice
and video calls may be made using the same encryption, with no long
distance fees. There are no advertisements or tracking in the
software. Signal is available for Android, iOS, Debian-based Linux,
macOS, and Windows, and may be built from source code for other Linux
and Unix-like platforms. In order to activate Signal, you must have
a public telephone number upon which you can receive an activation
code. This need not be the mobile number of the device on which you
run Signal, and may be a land line. Once you have activated Signal on
a mobile device, you can then pair your desktop to it. Signal has
been endorsed by Edward Snowden (who is a regular user of it) and by
security guru Bruce Schneier.
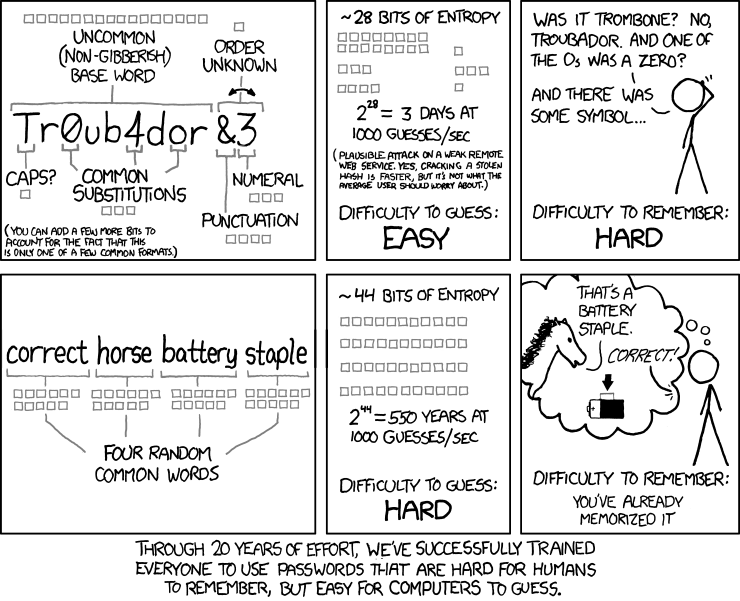
As noted in this xkcd cartoon, we've been encouraging people to make up and use gibberish passwords with the idea that they're harder to guess with an algorithm. This might have made sense in the bronze age, where due to limitations on storage, passwords were limited to eight or twelve characters or some such, but in the age of Extravagant Computing this makes no sense. The gibberish password is next to impossible to remember, which increases the probability it'll be written on a Post-it note stuck to the monitor or the bottom of the keyboard. It's far more secure to randomly choose a few words which can be easily remembered and entered without gymnastics on the keyboard (or even worse, from the on-screen keyboard of a mobile device). My JavaScrypt package (described in more detail below) includes a Pass Phrase Generator which (pseudo)randomly generates phrases chosen from a dictionary of 27,489 English words. If I request 5 words (equivalent to a key 73 bits in length), I might get, for example, “weight uranium demurral magazine gesso”. The Pass Phrase Generator runs entirely within the browser on your local computer: nothing is sent across the Internet, and you can run it (after having downloaded the Web page for offline access) without an Internet connection. Setting words to two and upper case only is great for generating names for covert missions and security compartments such as “LOLLIPOP PINCERS”.
Passwords are a pain, and despite endless promises that something better is on the horizon, we seem stuck with them forever. Despite the irritation, it's important not to succumb to the temptation of using the same password on more than one system. When you enter your password into an online system, you have no idea how securely it is stored there. (Competently-implemented systems store a “hash” of the password from which it is effectively impossible to recover the original password or discover an equivalent password which will generate the same hash, but competence is sadly rare among builders of online systems, and it seems like every couple of weeks we read of a large-scale breach which disclosed the passwords and personal information of a mass of innocent users.) At least, if you use a different password for each system, such a breach will only affect the one system which was compromised. But if you use the same user name and password on many systems, the attackers may be able to get into your accounts on the other systems before you learn of the breach and change your passwords all over the place (which is also a pain, especially if you haven't recorded all the systems on which you used that password).
Keeping all of these passwords straight is, of course, another irritation. Many browsers provide the option to remember passwords and fill them in automatically when you log in to a site, but you have to balance that convenience against the risk that if somebody gets physical access to the machine (including mobile devices which may be lost or stolen), they'll have all of your passwords at their disposal. Even more risky are browsers which offer to “sync” your saved passwords across all your devices by sending them back to headquarters. What a concept—disclosing all the passwords for all of your accounts: social media, financial, customer, etc. to Google! No thanks.
 An alternative means of juggling all
of these passwords is to use a
password manager utility. These
are programs which you install on one or more devices and into which
you enter all of your online account log-in credentials. Then, when
you need to access a site, you launch the password manager, usually
providing a master password, and it then fills in your user name and
password in the fields for the site. There are a lot of these
programs, so you'll need to choose one which runs on the platforms
you use and then read reviews to choose which best meets your
requirements. For many years, I have used a program now called
Codebook, which runs on macOS,
Windows, Android, and iOS, and encrypts its data with SQLCipher,
an open-source encryption package. It is able to synchronise via
a personal cloud storage account, not requiring a subscription from
its vendor. The vendor does not have a Linux desktop version, but
I have developed my own utility which reads its database and allows
me read-only access (which is all I need) on Linux machines. There
may be better alternatives available, but this one works for me.
An alternative means of juggling all
of these passwords is to use a
password manager utility. These
are programs which you install on one or more devices and into which
you enter all of your online account log-in credentials. Then, when
you need to access a site, you launch the password manager, usually
providing a master password, and it then fills in your user name and
password in the fields for the site. There are a lot of these
programs, so you'll need to choose one which runs on the platforms
you use and then read reviews to choose which best meets your
requirements. For many years, I have used a program now called
Codebook, which runs on macOS,
Windows, Android, and iOS, and encrypts its data with SQLCipher,
an open-source encryption package. It is able to synchronise via
a personal cloud storage account, not requiring a subscription from
its vendor. The vendor does not have a Linux desktop version, but
I have developed my own utility which reads its database and allows
me read-only access (which is all I need) on Linux machines. There
may be better alternatives available, but this one works for me.
 KeePassX
is a free, open source, cross platform password manager which runs on
Linux, macOS, and Windows desktop platforms. It securely encrypts
its databases and can export them from one platform and import them
to another. There is, however, no ability to automatically
synchronise multiple installations but, from the standpoint of
security, that may be a good thing.
KeePassX
is a free, open source, cross platform password manager which runs on
Linux, macOS, and Windows desktop platforms. It securely encrypts
its databases and can export them from one platform and import them
to another. There is, however, no ability to automatically
synchronise multiple installations but, from the standpoint of
security, that may be a good thing.
By the mid-2000s, I became dismayed at how few people bothered to take even the most rudimentary precautions in guarding their privacy, especially in an era where snooping by governments and services such as Gmail was becoming ever more intrusive. The most common response when I urged people to use packages such as the GNU Privacy Guard (described in detail below) was that they were difficult to install, complicated to configure, and inconvenient to use and, all in all, not worth the bother. This motivated me to create JavaScrypt, which is a comprehensive encryption package that runs entirely within a Web browser. All encryption and decryption are done locally, and nothing is sent over the Internet in the process. The package uses symmetric (secret key) encryption with the Advanced Encryption Standard and a 256 bit key, the algorithm adopted the U.S. federal government for its most secret data.
JavaScrypt is not a public key system. In order to securely communicate with a correspondent, you must first securely exchange a secret key, but thereafter it is very simple and easy to encrypt messages. You can then send these messages over insecure channels, for example, via Google Mail, confident they cannot be read without knowing the key. Encrypted messages are encoded in a variety of text formats so they can be sent over text-only channels including reading over the telephone or shortwave radio or transmitting in Morse code. Once you've downloaded JavaScrypt and installed it on your local computer, you can use it without a connection to the Internet.
 One of the first blows struck
against the snooper state was the release, in the early 1990s, of
Phil Zimmerman's
Pretty Good Privacy (PGP), which
evolved into a full-function public key cryptosystem with key
management, document signing, and key signing to create a web of
trust. Attempts by the U.S. government to block export of PGP and
prosecute Zimmerman for allowing the software to be exported via
the Internet were defeated when MIT Press published complete source
code of the software as a book, relying upon the First Amendment
protection of freedom of the press. After a long and complicated
series of twists and turns, the most widely used incarnation of this
software today is the independently-implemented but completely
compatible GNU
Privacy Guard (GPG), which is available in ready-to-run versions
for Linux, Windows, macOS, and Android, as well as source code which
can be built for other systems.
One of the first blows struck
against the snooper state was the release, in the early 1990s, of
Phil Zimmerman's
Pretty Good Privacy (PGP), which
evolved into a full-function public key cryptosystem with key
management, document signing, and key signing to create a web of
trust. Attempts by the U.S. government to block export of PGP and
prosecute Zimmerman for allowing the software to be exported via
the Internet were defeated when MIT Press published complete source
code of the software as a book, relying upon the First Amendment
protection of freedom of the press. After a long and complicated
series of twists and turns, the most widely used incarnation of this
software today is the independently-implemented but completely
compatible GNU
Privacy Guard (GPG), which is available in ready-to-run versions
for Linux, Windows, macOS, and Android, as well as source code which
can be built for other systems.
When you install GPG, you create a “key pair” consisting of a public and private key. You guard the private key carefully, but are free to distribute the public key, for example, posting it on your Web site. Anybody with the public key can send messages to you securely by encrypting them with it, and only you can read the messages, because only you have the private key required to decrypt them. Messages can be signed with your private key, providing powerful evidence that you are the author. GPG is a large, complicated software package, and many people find it intimidating when getting started, but once you've mastered the basics it's pretty easy to use, and you'll have access to encryption and authentication technology which is absolutely state of the art and completely free.
Once you generate a GPG key pair you can, if you wish, upload the public key to the OpenPGP key server so that people can send you encrypted messages without first contacting you and exchanging keys. For example, here is my public key (yes, this key is seventeen years old; aren't stable open standards wonderful?).
If you use public Internet access, for example WiFi in hotels, airports, or at conferences, your device is vulnerable to probes by any other device connected to that network, and you have no idea who may be snooping on your connection or logging what you're doing. If you travel to countries with dodgy security policies, restrictions on Internet access, or intrusive surveillance, you should be extra careful what you do. In the United States, it is now legal for Internet Service Providers (ISPs) to collect and sell your browsing history, so even if you have a direct connection to a “reputable” ISP, you can't be sure who's examining your browsing history. Some people, faced with these challenges, subscribe to a Virtual Private Network (VPN) service.
A VPN creates, via software you install on your computer (or mobile device), a secure, encrypted “tunnel” between you and the VPN's private network. Data sent over that tunnel are encrypted end-to-end and cannot be snooped or tracked, for example, by somebody on the local WiFi or by your ISP or upstream carrier. Your traffic passes through the VPN and emerges at an exit host, whence it crosses the Internet to its ultimate destination. The site you're accessing sees the access as originating from the VPN exit host—your IP address and location are completely hidden. Many VPN services allow you to select exit hosts in a wide variety of locations around the world, which may allow circumventing geographical restrictions imposed by Internet services (or, maybe not—Netflix, for example, has been on the warpath against VPNs which people were using to bypass their geographical restrictions, and blocking VPN exit hosts from accessing their services).
![]() I have never used a VPN because I
have a direct fibre optic connection to an enterprise-grade ISP
whom I trust, and I rarely if ever use public WiFi. Here is a
PC Magazine rating of
“The Best VPN Services for 2019”
just published in September, 2019. Their highest rating went to
NordVPN,
which seems to be the choice of a number of high profile users: they
have among the broadest client support and 5600 servers in 60
countries. Rated extremely highly for security is
ProtonVPN,
from the creators of ProtonMail, which has a
free
tier for users with limited requirements or who wish to try
the service before upgrading to a paid subscription.
I have never used a VPN because I
have a direct fibre optic connection to an enterprise-grade ISP
whom I trust, and I rarely if ever use public WiFi. Here is a
PC Magazine rating of
“The Best VPN Services for 2019”
just published in September, 2019. Their highest rating went to
NordVPN,
which seems to be the choice of a number of high profile users: they
have among the broadest client support and 5600 servers in 60
countries. Rated extremely highly for security is
ProtonVPN,
from the creators of ProtonMail, which has a
free
tier for users with limited requirements or who wish to try
the service before upgrading to a paid subscription.
 The
Tor Project was founded in 2006
to develop tools for providing privacy and anonymity on the Internet,
especially for those living under repressive regimes and journalists
reporting from within them. The Tor Network consists of a large
number of nodes (7521 active at this writing)
which forward encrypted messages among themselves between an entry
and exit node. The design of the network is such that only the
entry node knows the origin of the packet (but cannot decrypt its
contents), and only the exit node knows the content of the packet
(but cannot identify its source).
The
Tor Project was founded in 2006
to develop tools for providing privacy and anonymity on the Internet,
especially for those living under repressive regimes and journalists
reporting from within them. The Tor Network consists of a large
number of nodes (7521 active at this writing)
which forward encrypted messages among themselves between an entry
and exit node. The design of the network is such that only the
entry node knows the origin of the packet (but cannot decrypt its
contents), and only the exit node knows the content of the packet
(but cannot identify its source).
Several years ago, using Tor was a relatively involved process which involved setting up a server on your machine, then connecting to it as an Internet proxy. While you can still do this, most people who access the Web via a browser can simply use the Tor browser, which is a simple download for Linux, macOS, Windows, and Android, or you can use the Tor tab feature in desktop versions of the Brave browser.
If you use a mobile platform (mobile phone or tablet), many of the same security tools and techniques employed on desktop platforms can be used. There are, however, some special considerations for mobile platforms. First of all, they're mobile, which means they're more likely to be lost or stolen than a computer sitting on your desk at home or work. This means you should consider some form of access protection for the device (for example, a non-trivial pass code or phrase, fingerprint or facial recognition biometrics, or whatever) so its contents aren't an open book to whoever lays their hands on it. Most mobile operating systems provide a way to remotely erase the content or lock a lost or stolen device with a password known only to you. The time to learn about how this works for your device(s) is before the need arises.
The mobile market is, at present, pretty much divided between Apple's iOS and Google's Android operating systems, with the latter being used by a variety of hardware manufacturers. From the standpoint of security and privacy there isn't much difference between the systems: both are the products of large companies whose record in respecting the privacy of their customers is, shall we say, dubious. Both are part of an “ecosystem” in which their developers make the rules and control access by independent application developers to their customer base, sometimes banning products for political or commercial reasons. Here, I'd give the edge to Android, because unlike iOS, which makes it essentially impossible for third parties to deliver applications directly to users (who would have to “jailbreak” their devices and risk their being “bricked” by a subsequent iOS update), with Android it is possible to develop and install applications independently of the Google Play Store, which is more open to “edgy” applications (for example, aggressive ad blockers, encryption utilities, and cryptocurrency payment tools) than is Apple's App Store.
If you opt for iOS, Apple is the only hardware vendor, but in the Android market you have many choices. Be aware that Huawei, the number two worldwide in the smartphone market, is said to have deep ties to the Chinese Communist Party and People's Liberation Army, and that nobody can inspect the proprietary software they include on their phones. Regardless of the vendor, it's best to buy an unlocked mobile device in a sealed box from its manufacturer, even if it costs somewhat more. When you get a “subsidised” device from your mobile carrier, they may have pre-loaded it with spyware and adware which may be hidden and difficult to remove. Third party vendors present a risk of pre-installed malware infection.
Android is based upon open-source code, and there is a version of the operating system, called LineageOS, whose source code is open for inspection. It runs on more than 185 models of mobile devices, but installing and using it is very much like working with Linux around the year 2000, which means that if you aren't somewhat of a specialist in software and have a high tolerance for pain, it's probably not for you. There a free software repository, F-Droid, which is an alternative to the Google Play store, but the shelves are rather bare and you may not find what you need there.
On mobile devices, it seems like everybody with a Web site wants you to install their “app” which only talks to them. Sometimes they even go so far that when you visit their Web site from a browser on a mobile platform, they whack you in the face with a pop-up encouraging you to install the app. Why? Because it allows them to restrict, control, and track your interaction with them, and make it more difficult to check out the competition. Who needs that? Ignore the app and just use their Web site, just as you do on the desktop. Even if initially from a reputable source, every app presents a possible path for future malware introduction.
When you install mobile platform “apps” or launch them for the first time, some will ask you for permissions to access data on your device. Think before granting such permission: why does the app legitimately need it? Sure, an app which enhances photos you take with the camera needs access to the camera, but (an example I encountered not long ago) why does a musician's metronome want access to my Contacts? Well, probably in order to spam them trying to sell more copies. When you encounter such dodgy requests for access, the best approach is what I said to that metronome that ticked me off—you're fired!
Android comes with the Google Chrome browser and iOS with Apple's Safari, but you aren't restricted to using these snoopy tools. You can download and install Brave or the DuckDuckGo Privacy Browser (Android, iOS), and tell the snoopers to pound sand.
As you're a lot more likely to use a mobile device on a public WiFi network, it's worth considering whether it makes sense to subscribe to a Virtual Public Network (VPN) service as described above. Otherwise, you have no idea who may be snooping on what you do, for example, sniffing passwords for banking and other financial accounts.
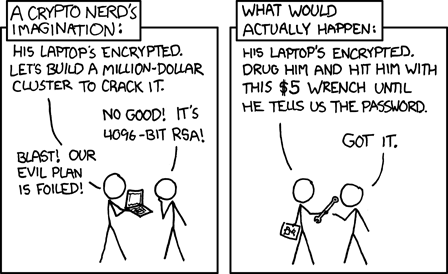
Remember that the best security tools won't protect you unless they're used correctly, and considered as a part of the total security solution. Unless you keep everything on your computer's bulk storage encrypted, anybody who can obtain physical access to the machine for half an hour can make a complete copy of its contents. And if you do encrypt all of bulk storage (which is not easy—I certainly wouldn't try it), when they're copying its contents they just install a hardware key logger to grab your password the next time you log in.
Multiple up-to-date backups of your systems, kept on read-only media and in multiple locations are as essential for security as protecting your data against hardware and software failures, burglary, fires, and bad asteroid days. Read-only media are those which can be written when backups are made, but not when accessed to restore the data recorded on them. These include tapes, such as the LTO media used to back up Fourmilab (which have a hardware write-inhibit on the tape cartridge), writable (but not erasable) optical discs, and external hard drives and USB memory units which can be mounted read-only when used to restore data.
Consider “ransomware”, where you're tricked into running software that encrypts all of your files and demands a large payment to deliver you the key to restore them. If you have current backups on read-only media (which the ransomware cannot write, and hence encrypt), you can simply clean your system of the infection and restore from the backups and you're back in business. There are many backup solutions available, including those that back up across the Internet to “cloud” storage (if you use one of these, make sure the backup is encrypted and that only you and those you trust have access to the key). The one I use is Bacula, a project I had a part in launching in the late 1990s, but this is enterprise-scale software which may be a bit much for individual users backing up a few of their own devices. (Bacula performs the nightly backups of fourmilab.ch and all of the development machines at Fourmilab.)